本文共 6946 字,大约阅读时间需要 23 分钟。
在上一篇文章中我们介绍了在Jenkinsfile中使用dockerfile来动态生成镜像,从而在指定的阶段进行使用。而对于将构建生成的二进制应用进行容器化,比如将spring boot应用的jar文件打包生成一个基于JRE或者JDK基础的镜像,这个可以使用docker.build来实现,这篇文章将继续结合示例来进行介绍。
环境准备
本文使用Easypack的LTS Jenkins 2.176.1版,环境准备请参看
- https://liumiaocn.blog.csdn.net/article/details/92764938
Registry 准备:
本文使用docker registry作为镜像私库的管理,环境准备只需如下一行语句即可执行命令:docker run -d -p 5000:5000 registry
使用docker ps确认私库管理的容器已经启动
liumiaocn:docker liumiao$ docker ps |grep registry06601f2782c0 registry "/entrypoint.sh /etc…" About a minute ago Up About a minute 0.0.0.0:5000->5000/tcp cocky_murdockliumiaocn:docker liumiao$
获取Jenkins-Crumb
使用如下示例代码获取Jenkins-Crumb,为使用API方式为示例作准备。
liumiaocn:jenkins liumiao$ jenkins_host_url=http://localhost:32002liumiaocn:jenkins liumiao$ user_passwd="root:liumiaocn"liumiaocn:jenkins liumiao$ jenkins_crumb=`curl -u $user_passwd ${ jenkins_host_url}'/crumbIssuer/api/xml?xpath=concat(//crumbRequestField,":",//crumb)' 2>/dev/null`liumiaocn:jenkins liumiao$ echo $jenkins_crumbJenkins-Crumb:6af0183fd58dea3d16f393b9e3272747liumiaocn:jenkins liumiao$ 创建Job
使用如下代码示例创建Job
liumiaocn:jenkins liumiao$ ls demo/pipeline/docker/registry/config.xmldemo/pipeline/docker/registry/config.xmlliumiaocn:jenkins liumiao$ cat demo/pipeline/docker/registry/config.xmlliumiaocn:jenkins liumiao$ curl -X POST -u $user_passwd -H ${jenkins_crumb} -H "Content-Type:application/xml" --data-binary "@demo/pipeline/docker/registry/config.xml" ${jenkins_host_url}/createItem?name=pipeline_job_registryliumiaocn:jenkins liumiao$ echo $?0liumiaocn:jenkins liumiao$ Pipeline Job Sample false false false
注:MYPASSWORD在实际运行是需要改成自己的密码,前面的liumiaocn是我的dockerhub的账号。
Jenkinsfile说明
本文示例所使用的Jenkinsfile信息如下所示,内容非常简单易读,简单说明如下:
- node是结构,在其中可以指定stage等信息
- stage为具体的节点,比如本文示例中模拟实际的准备Dockerfile、构建镜像等操作
- 本示例中使用了两种镜像推送的方式,第一种直接推送到前文准备的registry中,第二种推送到dockerhub上。
node { stage('Prepare Dockerfile') { sh 'cp /tmp/Dockerfile .' } stage('Build image and push to local registry') { docker.withRegistry('http://192.168.31.242:5000') { def nginx_img = docker.build('my-nginx:v1') nginx_img.push() } } stage('Build image and push to dockerhub ') { sh 'docker login -u liumiaocn -p MYPASSWORD' sh 'docker tag my-nginx:v1 liumiaocn/my-nginx:v1' sh 'docker push liumiaocn/my-nginx:v1' } } 执行Job
- Dockerfile准备 Dockerfile内容如下所示
liumiaocn:jenkins liumiao$ docker exec -it jenkins_jenkins_1 sh/ # cat /tmp/Dockerfile FROM nginx:latest/ #
- 事前确认
liumiaocn:jenkins liumiao$ docker images |grep my-nginxliumiaocn:jenkins liumiao$
使用如下命令或者直接在Jenkins上点击构建
liumiaocn:jenkins liumiao$ curl -X POST -u $user_passwd -H ${jenkins_crumb} ${jenkins_host_url}/job/pipeline_job_registry/buildliumiaocn:jenkins liumiao$ echo $?0liumiaocn:jenkins liumiao$ 确认执行结果
使用如下命令可以确认相关的执行日志信息
liumiaocn:jenkins liumiao$ curl -u $user_passwd ${jenkins_host_url}/job/pipeline_job_registry/1/consoleTextStarted by user rootRunning in Durability level: MAX_SURVIVABILITY[Pipeline] Start of Pipeline[Pipeline] nodeRunning on Jenkins in /data/jenkins/workspace/pipeline_job_registry[Pipeline] { [Pipeline] stage[Pipeline] { (Prepare Dockerfile)[Pipeline] sh+ cp /tmp/Dockerfile .[Pipeline] }[Pipeline] // stage[Pipeline] stage[Pipeline] { (Build image and push to local registry)[Pipeline] withEnv[Pipeline] { [Pipeline] withDockerRegistry[Pipeline] { [Pipeline] sh+ docker build -t my-nginx:v1 .Sending build context to Docker daemon 2.048kBStep 1/1 : FROM nginx:latestlatest: Pulling from library/nginx8d691f585fa8: Pulling fs layer047cb16c0ff6: Pulling fs layerb0bbed1a78ca: Pulling fs layerb0bbed1a78ca: Verifying Checksumb0bbed1a78ca: Download complete047cb16c0ff6: Verifying Checksum047cb16c0ff6: Download complete8d691f585fa8: Verifying Checksum8d691f585fa8: Download complete8d691f585fa8: Pull complete047cb16c0ff6: Pull completeb0bbed1a78ca: Pull completeDigest: sha256:77ebc94e0cec30b20f9056bac1066b09fbdc049401b71850922c63fc0cc1762eStatus: Downloaded newer image for nginx:latest ---> 5a9061639d0aSuccessfully built 5a9061639d0aSuccessfully tagged my-nginx:v1[Pipeline] dockerFingerprintFrom[Pipeline] sh+ docker tag my-nginx:v1 192.168.31.242:5000/my-nginx:v1[Pipeline] sh+ docker push 192.168.31.242:5000/my-nginx:v1The push refers to repository [192.168.31.242:5000/my-nginx]cf2436e84ea8: Preparinged4a4820ee08: Preparingb67d19e65ef6: Preparingcf2436e84ea8: Pusheded4a4820ee08: Pushedb67d19e65ef6: Pushedv1: digest: sha256:224f1b76ad5d6d5878c2dccba5b3dcc8e9a263ff04efdf0f8e0ef8f68c208a44 size: 948[Pipeline] }[Pipeline] // withDockerRegistry[Pipeline] }[Pipeline] // withEnv[Pipeline] }[Pipeline] // stage[Pipeline] stage[Pipeline] { (Build image and push to dockerhub )[Pipeline] sh+ docker login -u liumiaocn -p MYPASSWORDWARNING! Using --password via the CLI is insecure. Use --password-stdin.WARNING! Your password will be stored unencrypted in /root/.docker/config.json.Configure a credential helper to remove this warning. Seehttps://docs.docker.com/engine/reference/commandline/login/#credentials-storeLogin Succeeded[Pipeline] sh+ docker tag my-nginx:v1 liumiaocn/my-nginx:v1[Pipeline] sh+ docker push liumiaocn/my-nginx:v1The push refers to repository [docker.io/liumiaocn/my-nginx]cf2436e84ea8: Preparinged4a4820ee08: Preparingb67d19e65ef6: Preparingb67d19e65ef6: Mounted from library/nginxcf2436e84ea8: Mounted from library/nginxed4a4820ee08: Mounted from library/nginxv1: digest: sha256:224f1b76ad5d6d5878c2dccba5b3dcc8e9a263ff04efdf0f8e0ef8f68c208a44 size: 948[Pipeline] }[Pipeline] // stage[Pipeline] }[Pipeline] // node[Pipeline] End of PipelineFinished: SUCCESSliumiaocn:jenkins liumiao$ blueocean构建结果确认
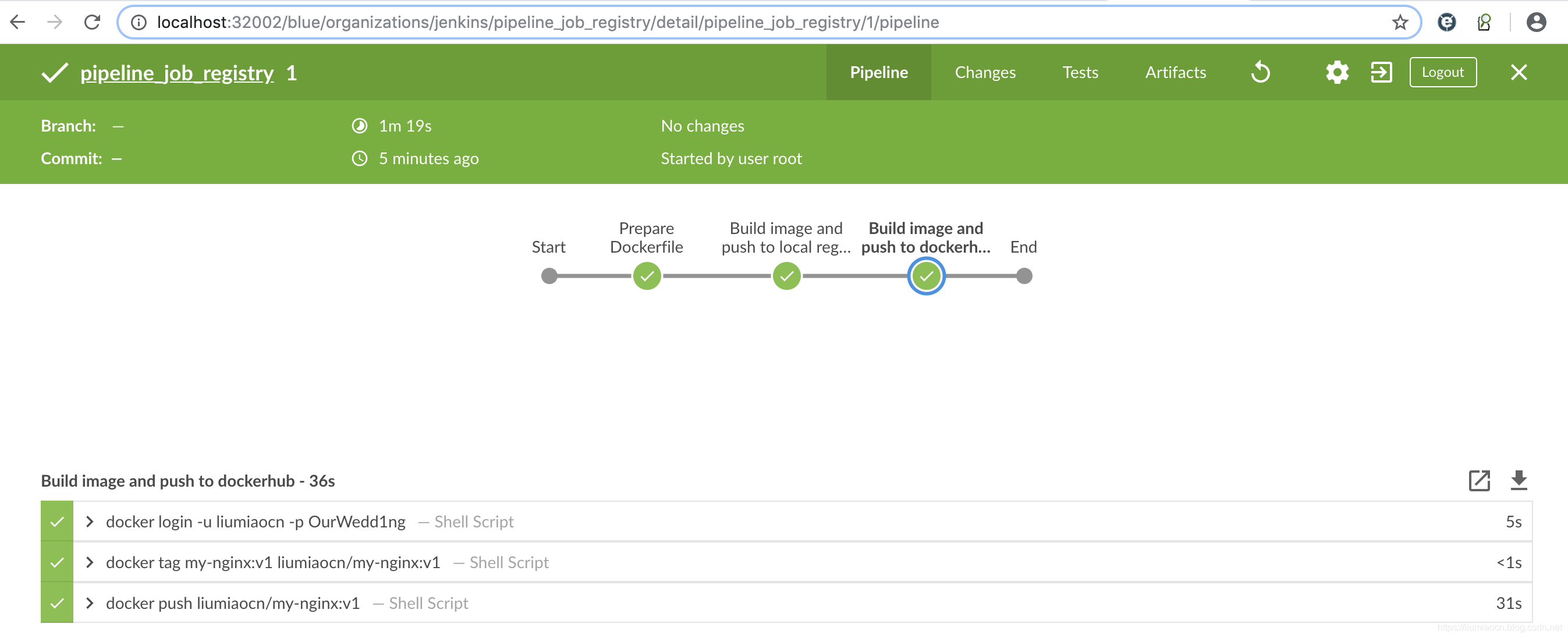
构建后镜像确认
liumiaocn:jenkins liumiao$ docker images |grep my-nginx192.168.31.242:5000/my-nginx v1 5a9061639d0a 2 days ago 126MBmy-nginx v1 5a9061639d0a 2 days ago 126MBliumiaocn/my-nginx v1 5a9061639d0a 2 days ago 126MBliumiaocn:jenkins liumiao$
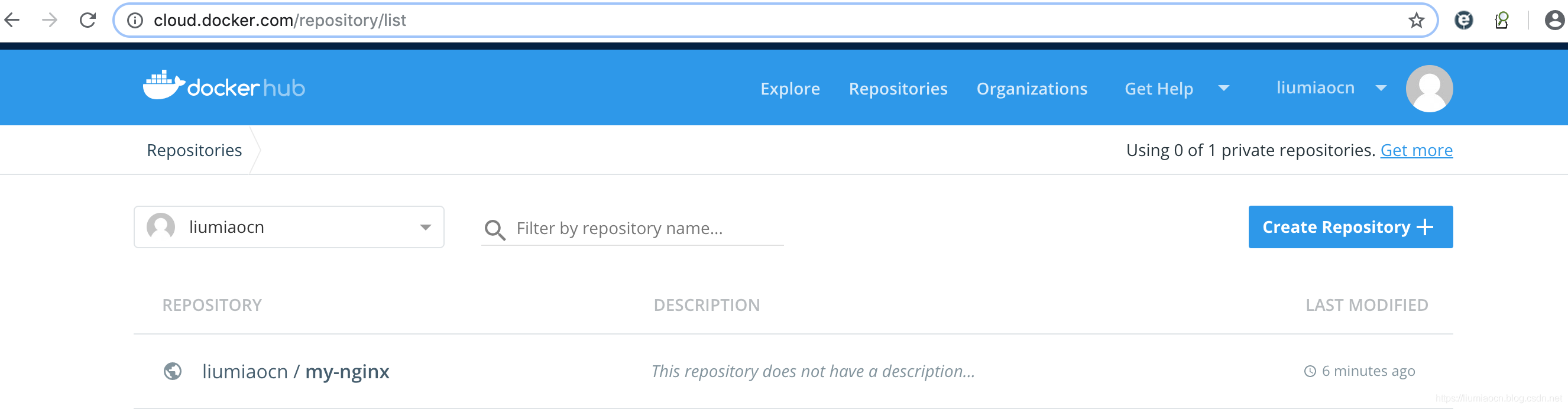
- Dockerhub镜像确认
注意事项
环境准备的docker-compose.yml中需要包含如下内容,以保证能够以容器方式运行的Jenkins能够进行镜像的生成。
- /var/run/docker.sock:/var/run/docker.sock 为了保证Jenkins-Crumb能够正常获取,不要设定如下Jenkins收起启动跳过插件内容的设定,以保证API的正常执行。 JAVA_OPTS=-Djenkins.install.runSetupWizard=false 另外,需要将registry的内容进行设定,否则在push时会出现下列类似的错误信息
Get https://192.168.31.242:5000/v2/: http: server gave HTTP response to HTTPS client
对应方法:
在linux下,可以在/etc/docker/daemon.json中添加registry的信息,重启docker服务即可。{ "insecure-registries":["192.168.31.242:5000"] } 在macOS上,则可以直接在GUI页面设定之后Apply,然后重启docker服务即可
参考内容
https://jenkins.io/doc/book/pipeline/docker/
转载地址:https://liumiaocn.blog.csdn.net/article/details/102633297 如侵犯您的版权,请留言回复原文章的地址,我们会给您删除此文章,给您带来不便请您谅解!
发表评论
最新留言
关于作者
